The exhibition “Out of Control – What the Web knows about you” calls us in mind since April 2012 what governments and companies do with our data and tracks on the Web. FH-Prof. DI Robert Kolmhofer of Upper Austria University of Applied Sciences Campus Hagenberg explains how we can best protect our data and he presents its 10 top links about the topic “Internet security”.
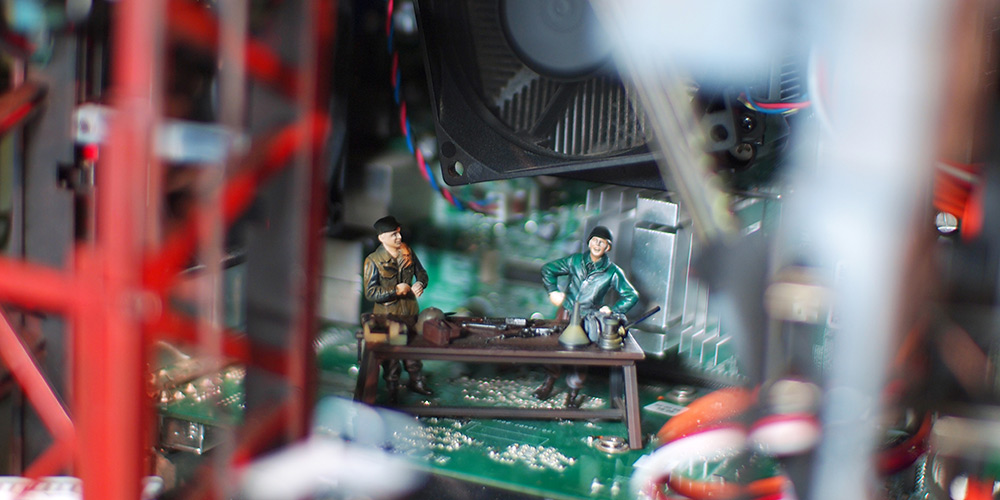
Play figures guard the data of the artist Hiroto Ikeuchi (JP) in the exhibition “Out of Control”
After the unveilings of the U.S. whistleblower Edward Snowden it is obvious that the anonymity of systems such as the TOR network, which had previously been considered as tap-proof, can not be guaranteed anymore. Surfing anonymously the web – is this actually still possible?
The documents show that – especially because TOR – surfing anonymously is easier nowadays than before. The means to do so are – at least for us – easily available. The TOR network is currently still robust. Individual but not enough TOR nodes can be attacked. And this is just the concept of how TOR is designed: Individual components of the TOR network may be unsafe without compromising the security of the whole system. But like every other system TOR is also vulnerable. The most likely reason why surfing anonymously is not possible with TOR will be errors caused by the user him- or herself. Personal information are not suitable for TOR sessions; TOR browser must not store cookies, outside of TOR a different browser should be used. Protecting yourself against attacks is actually a difficult task, since attacks – in particular trojans, keyloggers and so on – at all levels are possible.
What can I do to encrypt my e-mails to ensure that only the right recipient can read the contents? How to install this software? And does this slowdown the system?
One possibility for the encryption of e-mails is the use of PGP (Pretty Good Privacy). All the necessary downloads and instructions you will find for example free on www.gnupt.de. The installation will run automatically. The writing and reading of e-mails will be slower with one click. It is important to note that the most common e-mail clients do not support PGP by default. The corresponding extensions must therefore be installed on each system where you want to use encryption. Also on smartphones and tablets, there may be problems with PGP. As often the on-board appliances can be used to create signed and encrypted messages in iOS or Android. In addition, e-mail clients such as Outlook support the encryption and signing of e-mails via S/MIME. Instructions can be found here.
Wie merken Sie sich Ihre Passwörter? If we use the Web, we have to use user names and passwords for various services. Using the same password more than once would be a high risk for identity theft. And as the “password hacker” in the exhibition “Out of Control” shows, complicated strings are best. How do you remember your passwords?
As a base I use a word or two. The best words are not available as combination in the dictionary and which are not widespread. Dialect or spelling errors are perfect. Then I put my rules set for a unique structural change. So I write, for example, All vOwEls In UppEr cAsE lEttErs. Or I replace all “a” with “@” or “i” with “!”. Then I add a combination of special characters or numbers (eg “+13”) which I insert always after the third character or end of the word. So the Austrian dialect word “hoamatland” will be transfered to “hO@m@tl@nd+13”. This is easy to remember. And then I add after a defined set of rules the description of each web service to the password. So I have a separate password for each services. For Amazon “hO@m@tl@nd+13: Amaz”, for Google “hO@m@tl@nd+13:Goog”.

Can your own PC transform to a secure fortress?
Many of us think of antivirus protection on the own PC, but how much do I have to protect my phone? Is that possible?
There are various antivirus products for Android and now also for iOS. Experts do not agree of whether you need a virus scanner on the smartphone or tablet or not. Unfortunately, the various reviews about the products give a mixed image regarding the quality of detection. For Apple/iOS on the current state there are no useful products available and the recognition rate is more than bad. And there is virtually no malicious software. On Android, the situation is slightly different, there are indeed some “malicious” apps. It is important when using a virus scanner in any case, that it is a product of an approved company. Keep your hands away of freeware or trial versions that can be even “malicious software”. It is also important that there are regular updates for the virus scanner that you have to install. It is very important to install only apps that you will need and to look if there are any security holes or other defects known about your app you want to install or buy. A Google search always helps. Reviews can also be a good indication for the level of security of the app.
Digital data is copied quickly and once it is stored in the cloud or on servers outside of my four walls, I personally have no control over it. How do I protect my data?
Use only encrypted data for the cloud and only store data there when you do not matter if they fall into the wrong hands – but since you can have things then also put on Facebook. Well suited for this purporse are ZIP/RAR archives that you can encrypt with a strong password – with WinZIP, WinRAR or 7-Zip – and then store it in the cloud. But it is even safer to simply not use the cloud services.
The 10 best links for “Security on the Web”.
Official IT security info page of the Austrian government with target group-specific topics. Very informative and really useful for all situations.
Austrian Information Security Manual, created by the Austrian Government and available for free
“The source” in German-speaking countries for all topics related to information security
The “first CERT” (CERT = Computer Emergeny Response Team) with many recent security alerts in the IT sector (for experts)
The Austrian version of a CERT info
Database of known weak points in IT systems (more for experts)
Also a good source of information about security vulnerabilities
Homepage of our departments at the FH with information about studying, news, events, …
http://www.microsoft.com/security/default.aspx
Security tips by Microsoft
http://technet.microsoft.com/en-us/security/dn440717
Technical security homepage of Microsoft
http://support.apple.com/kb/ht1222
Apple security update infos
http://developer.android.com/guide/faq/security.html
Security infos for Android. Unfortunately not very helpful because the software creators are responsible for updates
At SAT February 8 and SUN February 9, 2014, the “Science Days” of the Ars Electronica Center will present the exhibition “Out of Control – What the Web knows about you” with lectures and tours about this hot topic of surveillance and Internet security.
